🌐 Clear Web vs Deep Web vs Dark Web: What’s the Real Difference?
The internet isn’t just what you see in your browser.
Behind every Google search lies a much larger digital ecosystem made up of three major layers:
- The Clear Web
- The Deep Web
- The Dark Web
Understanding the difference between them is critical for anyone working in IT, cybersecurity, privacy research, or digital infrastructure.
Let’s break it down properly — without hype.
🌎 The Clear Web (Surface Web)
The Clear Web is the portion of the internet that:
- Is indexed by search engines
- Is publicly accessible
- Requires no special software
If you can find it through Google, it’s part of the Clear Web.
Examples include:
- Wikipedia
- Amazon
- News websites
- Public blogs
- Corporate homepages
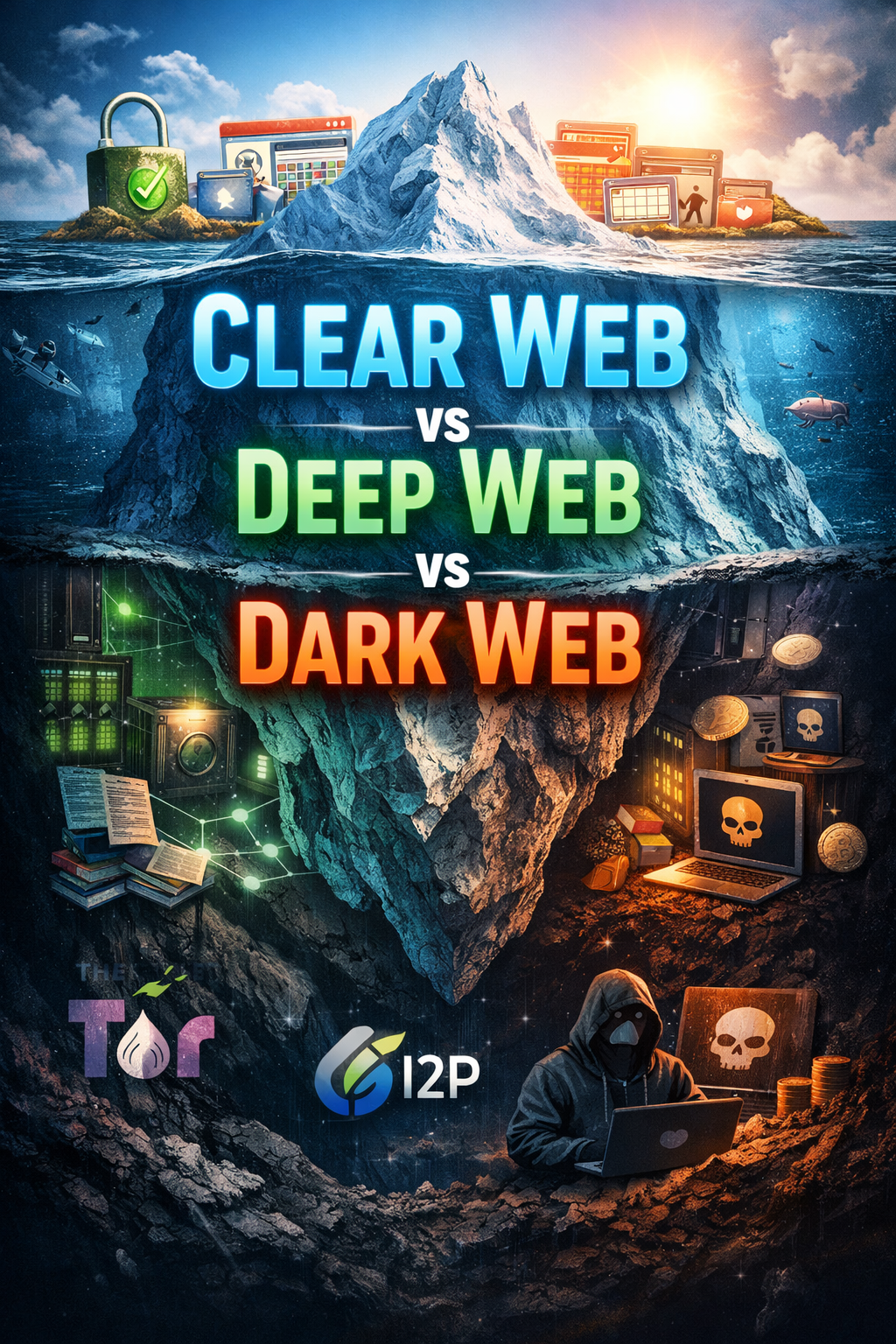
This is the “visible tip of the iceberg.”
Estimates suggest the Clear Web makes up less than 10% of the total internet.
🔒 The Deep Web
The Deep Web refers to content that is not indexed by search engines.
This does NOT mean illegal.
It simply means access-controlled.
Examples include:
- Online banking portals
- Email inboxes
- SaaS dashboards
- Private company systems
- Academic research databases
- Cloud storage accounts
If a webpage requires:
- Authentication
- A private link
- A subscription
- Special permissions
…it’s part of the Deep Web.
Most of the internet actually lives here.
The Deep Web is mostly normal, legitimate, and business-critical infrastructure.
🕶 The Dark Web
The Dark Web is a small, intentionally hidden portion of the Deep Web that requires specialized software or networks to access.
Unlike the Deep Web, it is built specifically for anonymity.
The most well-known access method is:
- Tor
Tor routes traffic through multiple encrypted relays to obscure the origin of the connection.
Websites accessed through Tor often use .onion domains.
Another privacy-focused network is:
- I2P
I2P (Invisible Internet Project) operates differently from Tor:
- It focuses more on internal anonymous services
- Uses garlic routing (bundled encrypted messages)
- Emphasizes peer-to-peer communication
Both Tor and I2P are anonymity networks — but they differ architecturally.
What Exists on the Dark Web?
The Dark Web contains both legitimate and illicit activity.
Legitimate Uses
- Journalists protecting sources
- Whistleblower platforms
- Activists in authoritarian countries
- Privacy-first communications
- Secure research environments
Example:
- ProPublica operates a Tor site for secure submissions.
Illicit Uses
- Black markets
- Stolen data marketplaces
- Malware distribution
- Fraud services
The network itself is not illegal — but some users abuse its anonymity.
🔐 Privacy vs Security: They Are Not the Same
This is where confusion often happens.
Privacy
Privacy focuses on hiding identity and activity.
Tor and I2P prioritize privacy by:
- Masking IP addresses
- Obscuring routing paths
- Preventing traffic correlation
Privacy answers:
“Can someone see who I am?”
Security
Security focuses on protection from compromise.
Security answers:
“Can someone intercept, modify, or impersonate communication?”
You can have privacy without strong security.
You can have security without anonymity.
They overlap — but they are not identical.
🔏 TLS Certificates and Identity Verification
On the Clear Web, security and identity are reinforced using TLS certificates.
When you visit:
https://example.com
Your browser verifies:
- The certificate chain
- The issuing Certificate Authority (CA)
- Domain ownership
TLS helps ensure:
- Encrypted communication
- Authentic server identity
- Protection against man-in-the-middle attacks
This model works because:
- Trusted Certificate Authorities exist
- Domain ownership is verifiable
- Public infrastructure supports identity validation
⚠ Why TLS Doesn’t Fully Solve Dark Web Identity
On the Dark Web:
- There is no traditional DNS
- There is no public Certificate Authority system
- There is no standard identity framework
Tor .onion addresses are derived from cryptographic keys.
While this provides cryptographic verification of the service itself, it does NOT guarantee:
- Who operates the service
- Whether the operator is trustworthy
- Whether the service was socially engineered
You may be cryptographically connected to a hidden service —
but you may not know who is behind it.
This creates a fundamental limitation:
Encryption does not equal identity assurance.
In contrast to the Clear Web, where TLS ties domains to organizations via CAs, the Dark Web relies primarily on key-based trust and reputation.
That changes the threat model entirely.
🧠 The Iceberg Analogy (Correctly Explained)
Think of the internet like this:
- Clear Web → Publicly searchable layer
- Deep Web → Private, access-controlled systems
- Dark Web → Intentionally anonymous overlay networks
The Dark Web is not “deeper” — it is structurally different.
It is an overlay network built on top of the internet.
🚨 Common Misconceptions
❌ Deep Web = Dark Web
False.
❌ Dark Web = 100% illegal
False.
❌ TLS guarantees identity everywhere
False.
❌ Anonymity means safety
Dangerously false.
⚖ Risk Reality
The Dark Web is not inherently evil.
But it removes many of the identity verification mechanisms we rely on in traditional web infrastructure.
When identity verification weakens:
- Impersonation risk increases
- Social engineering becomes easier
- Trust becomes decentralized
This is why operational security (OpSec) matters significantly more in anonymous environments.
Final Thoughts
Understanding the differences between:
- Clear Web
- Deep Web
- Dark Web
…is essential in cybersecurity discussions.
Privacy networks like Tor and I2P offer powerful anonymity tools.
But anonymity is not identity.
Encryption is not trust.
Privacy is not security.
Knowing the difference is what separates curiosity from competence.
About the author
Tim Wilkes is a UK-based security architect with over 15 years of experience in electronics, Linux, and Unix systems administration. Since 2021, he's been designing secure systems for a telecom company while indulging his passions for programming, automation, and 3D printing. Tim shares his projects, tinkering adventures, and tech insights here - partly as a personal log, and partly in the hopes that others will find them useful.
Want to connect or follow along?
LinkedIn: [phpsytems]
Twitter / X: [@timmehwimmy]
Mastodon: [@timmehwimmy@infosec.exchange]
If you've found a post helpful, consider supporting the blog - it's a part-time passion that your support helps keep alive.
⚠️ Disclaimer
This post may contain affiliate links. If you choose to purchase through them, I may earn a small commission at no extra cost to you. I only recommend items and services I’ve personally read or used and found valuable.
As an Amazon Associate I earn from qualifying purchases.